Scan Uploaded Files For Viruses Php
Just be careful. If your clamscan becomes outdated you'll get feedback in the output: It will look like this: LibClamAV Warning: *********************************************************** LibClamAV Warning: *** This version of the ClamAV engine is outdated. *** LibClamAV Warning: *** DON'T PANIC!
Read *** LibClamAV Warning: *********************************************************** Also depending on the version of clamscan the 'result' might look like this (and you'll need to parse it accordingly): [filename]: OK ----------- SCAN SUMMARY ----------- Known viruses: x Engine version: x.x. Gambaran Pemrograman Web Php Stok Barang Sederhana. x Scanned directories: 0 Scanned files: 1 Infected files: 0 Data scanned: x.xx MB Data read: x.xx MB (ratio 0.00:1) Time: x.xx sec (0 m x s).
The ability to upload files on a website is a common feature, often used to enable users or customers to upload documents and images. While this is useful in many situations, the security implications of hosting a file-upload facility are significant. Here are some. Malicious file uploads An ordinary user may use the facility to upload the type of files expected. However, an attacker could take advantage of the facility with. There are two fundamental ways a website can be attacked by a file upload. Scanner Driver For Hp Laserjet M1136 Mfp more.
The first way involves the type of file uploaded. A file could overwrite another file that already exists with the exact same name on the server. If this were a critical file, the new file could cause the website to function incorrectly, or not at all. The new file could be used to deface the website by replacing an existing page, or it could be used to edit the list of allowed file types in order to make further attacks simpler. The second way a website could be attacked by involves the content of the uploaded file. The uploaded file could contain malicious code in the form of an exploit, virus, Trojan or malware, which could be used to gain control of the Web server. For example, it is possible to hide PHP code inside an image file and still have it appear to be an image.
When the image is opened, it also executes the code hidden in the file. The file could contain scripts or tags that exploit other well-known Web application vulnerabilities, such as.
How To Automatically Scan Uploaded Files For Viruses With php-clamavlib Tweet Follow @kreationnext That way you can make sure that your upload form will not be abused to distribute malware.
Alternatively, the file space of the Web server could be exhausted by the attacker uploading a huge file. If the uploaded file can be accessed by entering a specific URL path, it could be especially dangerous because the file could be executed immediately after uploading. Defending against file upload attacks There are six steps to protecting a website from. • The application should use a of allowed file types. This list determines the types of files that can be uploaded, and rejects all files that do not match approved types.
• The application should use client- or server-side input validation to ensure evasion techniques have not been used to bypass the whitelist filter. These evasion techniques could include appending a second file type to the file name (e.g. Image.jpg.php) or using trailing space or dots in the file name. • The application should set a maximum length for the file name, and a maximum size for the file itself.
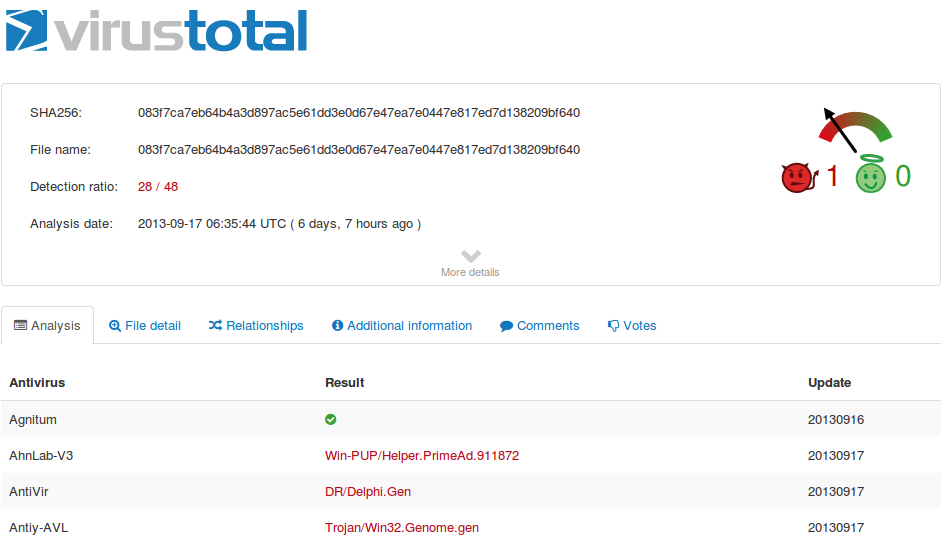
• The directory to which files are uploaded should be outside of the website root. • All uploaded files should be scanned by before they are opened. • The application should not use the file name supplied by the user. Instead, the uploaded file should be renamed according to a predetermined convention. Descargar Operation Flashpoint Red River Crack. While these techniques cannot guarantee a website will never be attacked from a malicious file upload, they will go a long way toward protecting the website while still providing users with the benefits of uploading files when needed.
Related Q&A from The OneOps cloud application lifecycle management tool helps organizations regain control of cloud deployments and prevent vendor lock-in. A brute force login attack can enable an attacker to log in to an application and steal data. Rob Shapland explains how to prevent brute force. Do your Web app users upload files to your servers? Find out the dangers of malicious file uploads and learn six steps to stop file-upload attacks. Read more on Hackers and cybercrime prevention.